
Viewpoints | May 27,2023
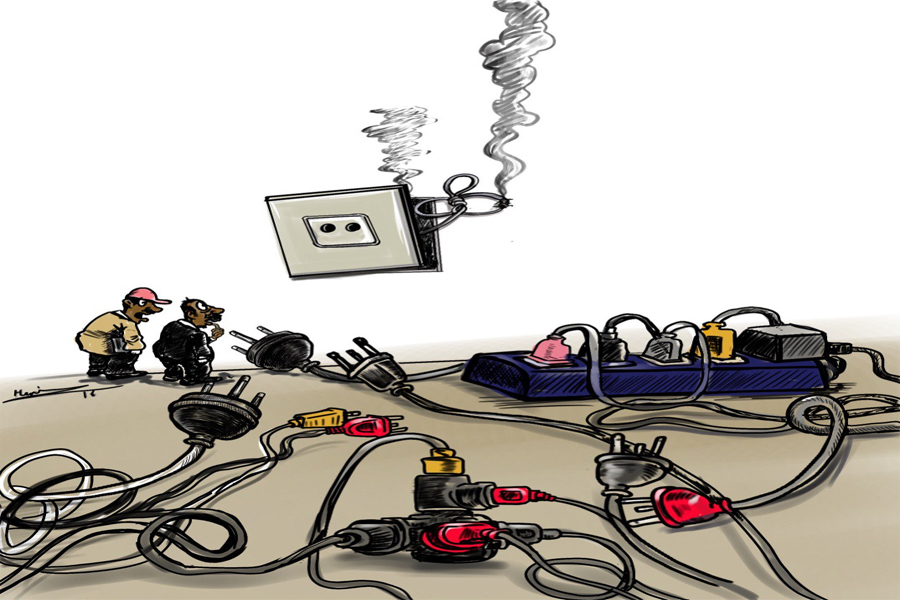
Standing in front of my house, I mused at the utility technicians with their pickups and ladders, going up and down poles, busy connecting households.
“Is everything being connected and that connection maintained every single moment now?” I said to myself.
Just a little while ago, I shared a piece from my life, as a writer aspirant, to a group of book lovers on my Facebook page.
A little while later, I received a friend suggestion from the social media platform of someone I have not seen in more three decades. I did not search for the person, and neither was a friend request sent to me. Facebook “guessed” I might know that person.
It sent a chill up my spine just considering the privacy implications of this. The platform has gathered enough information about the people in my circle to correctly predict my interests and even history.
Is this a fair price to pay to be connected? What does social media – or just communications technology as a whole – offer in return for such private pieces of our information?
It does, in fact, have a great deal to offer. To know what, all one has to do is remember life in a time before the internet, or even when telephones were not that widespread in Addis Abeba.
It is with nostalgia that I remember the first day a landline telephone pole was erected in my neighbourhood when I was but an infant. It was embraced and endearingly kissed by elated grownups.
For decades, that technology remained rickety. Take my time working in fieldwork, a couple of decades back. We would pick up a phone, wait for the operator to answer, or would roll the lever to ring a bell, and then tell the operator who we wanted to be connected with. Every phone call that was made had to be put through by hand. There was no automatic switch for calls coming in from out-of-town areas.
A computer was a gadget that was even more out of reach. My first seven years of public service never allowed me to have a closer look at a computer. The next year did, and I immediately moved to the private sector. Being hooked to the net from my office desk, I cannot forget the rush of excitement as the computer opened.
We were embarking on a new brave world, and many of us were thrilled by it but not necessarily satisfied. There were a couple of guys I met in pub 16 years back. One was a senior citizen to whom a computer meant his whole life and a younger one in his late twenties. I related my astonishment at the ongoing IT revolution. They could not believe this that I really thought it was a “revolution” considering the quality of service in Ethiopia.
As a response to my bewildered look, the older man started to tell us about his wrenching days as a four-digit salaried computer engineer, which afforded him life in a posh apartment, with a high life in the area known as Mosvold in Piassa.
Then, he continued lamenting about how poor infrastructure in Ethiopia distanced him from his beloved field. Then the youngster started to complain of the sluggish dial-up connections of the day and listed the absence of alternative services. Yet, for all his objections, he said life without the fruits of the information age is unthinkable.
It is not always that I agree with such sentiments. Indeed, it takes me a long time to catch up, as my long-lasting iPhone 4, a version of the iPhone lineup released a decade ago, testifies. To test how updated I am with prevailing mobile devices, as well as ceremoniously retiring my iPhone 4, which served me for a decade, I headed to an IT professional, who has a shop very close to my house.
As he started listing the options out there in the market, the virtue he repeatedly underlined about quality revolved around the devices’ security features. As the list was long and he was busy, I told him I would return some other day and headed home as I was obsessed with his concern.
The urgency for security is indeed an urgent concern that should get the appropriate intervention. These are the machines that allow us to essentially deport a digitised version of ourselves into extremely interconnected computing systems. We are unloading a great deal of our information that is later used to draw all sorts of conclusions as well as help us make choices, including how we pay our bills, elect our presidents or even find our life partners.
We are sharing with the assumption of confidence. It should not be betrayed lest the communications technology, which has come this far, loses its edge.
PUBLISHED ON
Nov 14,2020 [ VOL
21 , NO
1072]


Viewpoints | May 27,2023

Radar | Jun 27,2020

Fortune News | Mar 07,2020

Commentaries | Feb 27,2021

Commentaries | Oct 16,2020

My Opinion | Jan 07,2022

Viewpoints | Apr 28,2024

Radar | Dec 14,2019

Life Matters | Sep 04,2021
Editorial | Jul 30,2022

Jul 13 , 2024 . By AKSAH ITALO
Investors who rely on tractors, trucks, and field vehicles for commuting, transportin...

Jul 13 , 2024 . By MUNIR SHEMSU
The cracks in Ethiopia's higher education system were laid bare during a synthesis re...

Jul 13 , 2024 . By AKSAH ITALO
Construction authorities have unveiled a price adjustment implementation manual for s...

Jul 13 , 2024
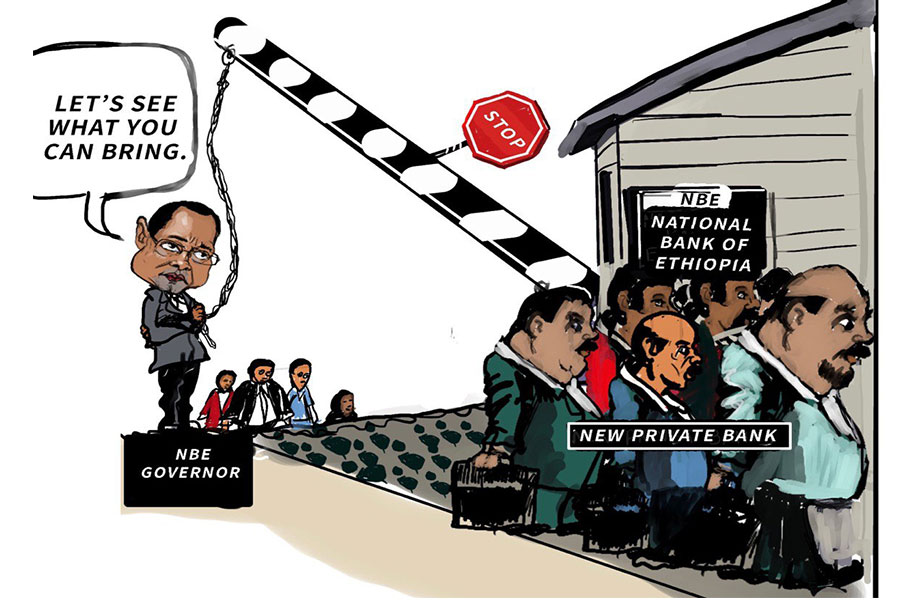
The banking industry is experiencing a transformative period under the oversight of N...
Jul 20 , 2024
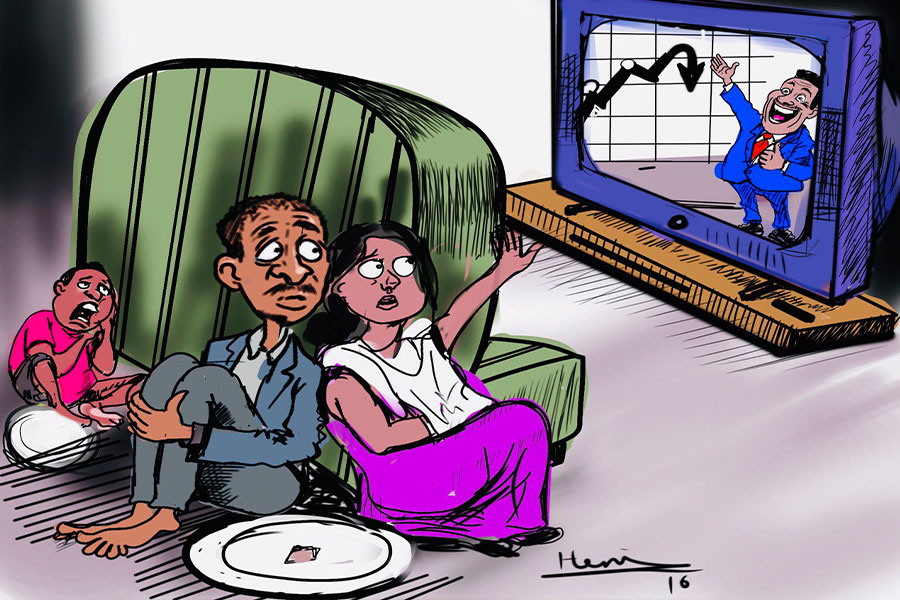
In a volatile economic environment, sudden policy reversals leave businesses reeling...
Jul 13 , 2024
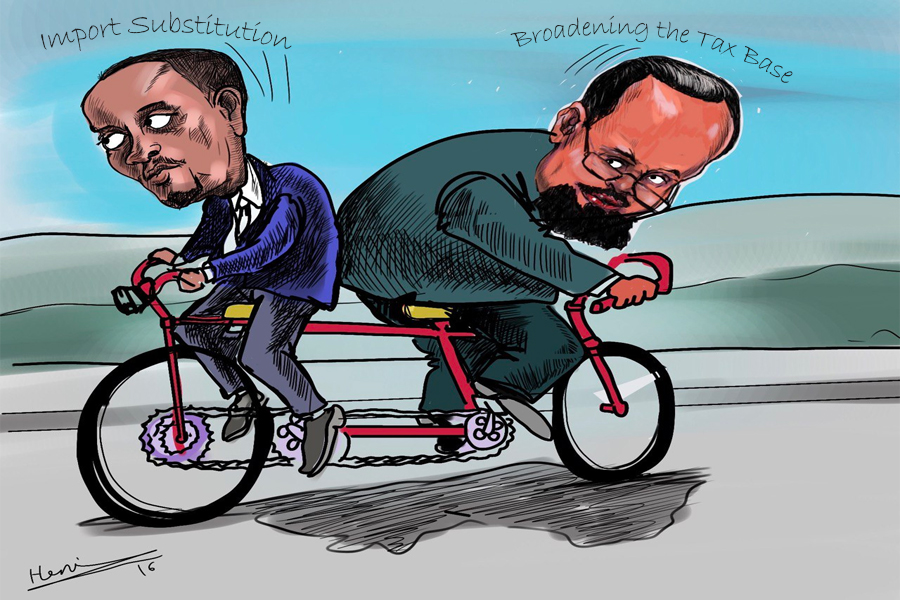
Policymakers are walking a tightrope, struggling to generate growth and create millio...

Jul 7 , 2024
The federal budget has crossed a symbolic threshold, approaching the one trillion Bir...
Jun 29 , 2024
In a spirited bid for autonomy, the National Bank of Ethiopia (NBE), under its younge...